Topics on this page
Integrate Workload Security with Trend Vision One
The extended detection and response (XDR) capabilities of Trend Vision One apply effective expert analytics and global threat intelligence using data collected across multiple vectors, such as email, endpoints, servers, cloud workloads, and networks.
To integrate XDR with Trend Cloud One - Endpoint & Workload Security, you need to register with Trend Cloud One. The method for registering with Trend Cloud One varies depending on whether you are using the Product Instance app or the Product Connector app.
Register with Trend Vision One using the Product Instance app XDR
You can register with Trend Vision One as follows:
-
Go to Service Management > Product Instance Management.
-
Obtain the enrollment token, as follows:
- Open the Trend Vision One console.
- Click Add Existing Product. Note that the token is only valid for 24 hours after it has been generated. If it expires, you need to generate a new token.
- On the Product Connection panel, select Trend Cloud One.
- Read the information displayed on the Product Connection panel.
- Copy the token.
-
On the Product Connection panel, click Open console to open the Trend Cloud One console.
-
On the Trend Cloud One console, go to Integrations > Trend Vision One and click Update with Enrollment Token.
- On the Update Enrollment Token dialog, paste the enrollment token and click Update.
Register with Trend Vision One using the Product Connector app XDR
You can register with Trend Vision One as follows:
- Go to Service Management > Product Connector.
- Click Connect.
- From the Product Name list, select Trend Cloud One.
- Click Save.
After registration has completed successfully, the Trend Cloud One portal displays the connection status of Trend Cloud One - Endpoint & Workload Security as Connected.
Note that after registering and connecting Trend Cloud One with Trend Vision One, Trend Cloud One - Endpoint & Workload Security is no longer available in the Trend Cloud One environment, as registering transfers all endpoint management to Trend Vision One in the Server & Workload Protection and Endpoint Inventory apps.
Alternatively, you can update Cloud One Workload Security to Trend Cloud One - Endpoint & Workload Security using the Trend Vision One console. For more information, see Update Cloud One Workload Security to Trend Cloud One - Endpoint & Workload Security.
Forward security events to Trend Vision One XDR
After successfully registering with Trend Vision One XDR, the Forward security events to Trend Vision One setting is enabled by default. When this configuration is enabled, events from the following protection modules are forwarded to the Trend Vision One XDR platform:
- Anti-Malware
- Web Reputation
- Device Control
- Integrity Monitoring
- Log Inspection
- Intrusion Prevention
- Activity Monitoring
To stop forwarding events, navigate to Vision One Administrator > Product Connector and disable Endpoint & Workload Security in Trend Cloud One. If you have connected your agents and relays to the primary security update source via a proxy, XDR automatically uses the same proxy settings.
Enable Activity Monitoring
Activity Monitoring is a security policy that takes your detection and response support to the next level, providing complete visibility of your workloads. When Activity Monitoring is enabled, the following activity information is forwarded to the Trend Vision One XDR platform:
- Process activity
- File activity
- Network activity
- Connection activity
- Domain query activity
- Registry activity (Windows only)
- User account activity (Windows and macOS only)
Activity Monitoring is supported on the agent version 20.0.0-1681 (20 LTS Update 2021-01-04) and later on Linux, Windows, and Unix. Activity Monitoring is supported on the agent version 20.0.0-158 (20 LTS Update 2022-07-11) and later on macOS.
To configure Activity Monitoring, perform the following:
- Before enabling Activity Monitoring, ensure that agents have outbound connectivity to the FQDNs related to XDR listed in the Workload Security URLs table. This is the network connection that the agents will use to send data to the XDR data lake.
- Follow the steps described in the previous sections of this document to register with Trend Vision One XDR and forward events to it.
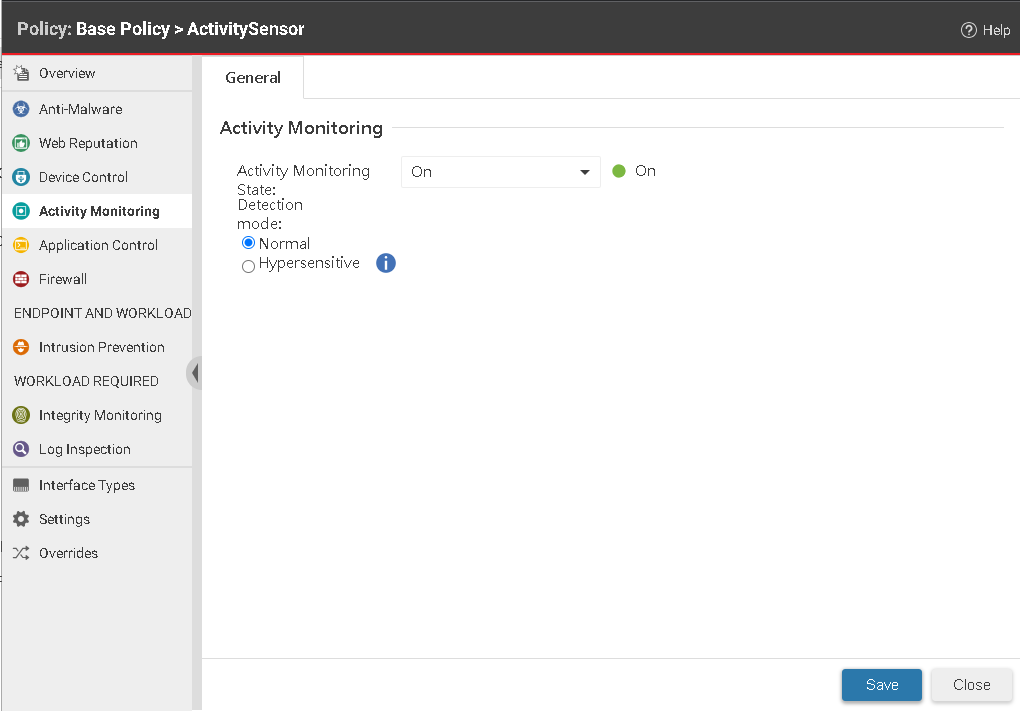
- Navigate to the Workload Security console and access Policies.
- Double-click the policy where you want to enable Activity Monitoring.
- Select Activity Monitoring > General.
- For Activity Monitoring State, select On, and then specify whether the threat detection mode should be Normal to provide regular detection or Hypersensitive for enhanced detection. Note that the latter is currently supported only on Windows.
- Click Save.
Activity Monitoring is now enabled and your activity logs are sent to Trend Vision One, providing better visibility and protection to your workloads.