Topics on this page
Set up a data center gateway
To enable Workload Security to get an inventory of your computers from your VMware vCenter or Active Directory servers, you must put a data center gateway between them, as shown in the following diagram.
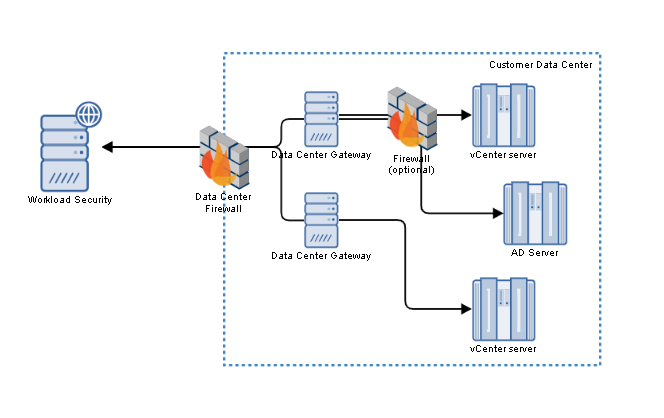
The data center gateway proxies the connections.
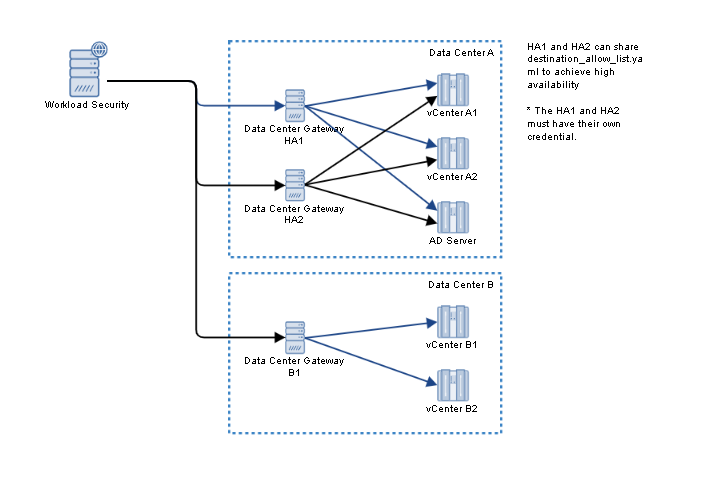
For high availability (HA) in case of network interruptions or component failures, you can also deploy multiple data center gateways, as shown in the following diagram.
Basic steps include:
- Verify system requirements
- Grant permissions
- Download the data center gateway software
- Download the credential files
- Configure the vCenter/Active Directory servers and proxies
- Install the data center gateway
Verify system requirements
Data center gateways are supported on the following platforms:
| Platform | Data center gateway version |
|---|---|
| Red Hat Enterprise Linux 7 | 1.0.45 and earlier |
| Red Hat Enterprise Linux 8 | 1.0.45 and earlier |
| Red Hat Enterprise Linux 9 | 1.0.51 and later * |
| Ubuntu Linux 18.04 | 1.0.45 and earlier |
| Ubuntu Linux 20.04 | 1.0.45 and earlier |
| Ubuntu Linux 22.04 | 1.0.51 and later * |
* If you try to install earlier versions of the data center gateway on this platform, you can run into known library compatibility issues. For information on how to resolve these issues, see Troubleshooting.
Minimum hardware requirements:
- 1 CPU or virtual CPU (vCPU)
- 2 GB memory (RAM)
- 1 GB free disk space
Firewalls and proxies must also allow network connections with required port numbers, host names, and IP addresses.
Grant permissions
During installation, you need to configure the data center gateway with its authentication credentials. Because these credentials do not belong to your user account, an administrator must grant special permissions to access them.
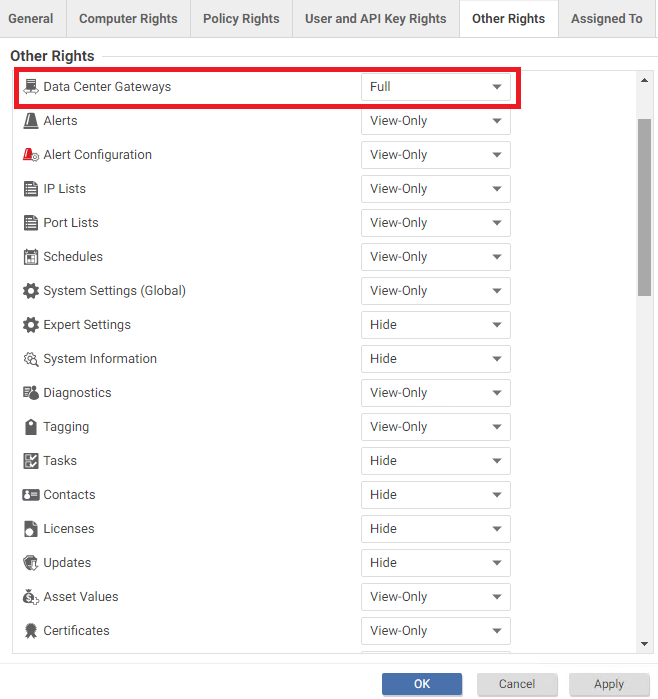
- On the Workload Security console, go to Administration > User Management > Roles.
- Edit the role of the user who will download credentials for the data center gateways.
- Select Properties > Other Rights. For Data Center Gateways, select Full.
Download the data center gateway software
For Red Hat Enterprise Linux, download an RPM file.
For Ubuntu, download a DEB file.
The FIPS package is intended for the government deployments of the data center gateway. This package is compatible with Ubuntu Pro FIPS 20.04 on AWS. To use this package, ensure that you have the Ubuntu FIPS for AWS | Ubuntu image with the FIPS package in your environment.
Download the credential files
Each credential file contains keys and identifiers that its data center gateway uses to authenticate and communicate with Workload Security.
- On the Workload Security console, go to Administration > System Settings > Data Center Gateway.
- Click New.
- Enter a Display Name.
- Click Next.
- Click Download Credential File. Do not change the name of the file. It is required by the installer.
- Repeat the previous steps to download one credential file for each data center gateway that you install.
Only use a credential file with its own data center gateway. Even data center gateways that are deployed as HA pairs have unique credential files. Copying the same file to multiple installations could lead to unexpected behavior. In addition, keep the credential files in a secure place and use permissions to restrict access. Keys are secrets, similar to passwords. Unauthorized access can result in security compromise.
Configure the vCenter and Active Directory servers and proxies
During installation, you need to provide a list of VMware vCenter or Microsoft Active Directory servers to which the data center gateway connects (if applicable to your setup). Use a plain text editor to write the list. The list must be in YAML format and named destination_allow_list.yaml.
Use a linter to verify that the list is in valid YAML format. Invalid files cannot be used by the installer.
Verify that the data center gateway can reach all network addresses in the list. If data center gateways must connect through a proxy to the Internet, or to the internal network's vCenter or Active Directory servers, then also configure the data center gateway to use the proxies.
For example, destination_allow_list.yaml could contain the following:
gateway_proxy:
- HostName: "internet.proxy.example.com"
Port: 3128
Username: "intenet_proxy_user"
Password: "internet_proxy_password"
destinations:
- HostName: "vcenter1.datacenter.internal"
Port: 443
- HostName: "192.168.123.45"
Port: 443
- HostName: "adserver1.datacenter.internal"
Port: 389
- HostName: "192.168.123.46"
Port: 389
Proxy:
HostName: "proxy.vCenter.internal"
Port: 3128
Username: "vcenter_proxy_user"
Password: "vcenter_proxy_password"Where:
-
The
gateway_proxysection defines the proxy that the data center gateway uses to connect to Workload Security. -
The
destinationssection defines the vCenter or Active Directory servers and the proxies used to connect to them (if any). -
HostNameis the identifier that is used to add vCenter or Active Directory servers in the Workload Security console or API.
Each HostName must be unique. If the domain name or IP address point to the same vCenter or Active Directory server as another HostName, it can cause unexpected behaviors on managed agents.
UsernameandPasswordare the login that the data center gateway uses to connect to a proxy. Omit them if no authentication is required.
Keep destination_allow_list.yaml in a secure place and use permissions to restrict access. It contains passwords. Unauthorized access can result in security compromise. In addition, remember that each HostName must be unique. If the domain name or IP address point to the same vCenter/Active Directory server as another HostName, it can cause unexpected behaviors on managed agents.
To prevent duplication if multiple HostName entries resolve to the same IP address, only the first domain name takes effect. Domain names take precedence over IP addresses. For example, given the following configuration, the data center gateway can communicate with a vCenter server at the hostname vc1.dc.internal:
# Both "vc1.dc.internal" and "vc1.dc.example.com" resolve to 192.168.100.1
destinations:
- HostName: "192.168.100.1" # Does not take effect because hostnames take precedence over IP addresses
Port: 443
- HostName: "vc1.dc.internal" # Takes effect
Port: 443
- HostName: "vc1.dc.example.com" # Does not take effect because it resolves to the same IP address as previous hostname
Port: 443Install the data center gateway
On the server where you want to install the data center gateway, upload the installer, authentication credentials, and configuration file, and then enter the installer command:
- On Red Hat Enterprise Linux:
sudo DCGW_CRED_PATH="</absolute/path/to/credentials.json>" DCGW_ALLOW_LIST_PATH="</absolute/path/to/destination_allow_list.yaml>" rpm -ivh /path/to/rpm/file - On Ubuntu:
sudo DCGW_CRED_PATH="</absolute/path/to/credentials.json>" DCGW_ALLOW_LIST_PATH="</absolute/path/to/destination_allow_list.yaml>" apt install /path/to/deb/file
If any of the following error messages appear, correct the problem and try again.
| Error Message | Possible Cause | Solution |
|---|---|---|
File path for credentials.json is required, please set the variable DCGW_CRED_PATH to proceed |
The parameter DCGW_CRED_PATH was not assigned during installation. |
Set the variable DCGW_CRED_PATH with the complete path of the credentials.json file. |
| File name should contains credentials or destination_allow_list file extension | DCGW_CRED_PATH or DCGW_ALLOW_LIST_PATH does not contain the required file name. |
Verify that the value of DCGW_CRED_PATH ends with the file name credentials.json,
and the value of DCGW_ALLOW_LIST_PATH ends with the file name destination_allow_list.yaml.Do not modify these file names. |
No such file, please use readlink -f to get absolute path for credentials.json or destination_allow_list.yaml |
The given path for DCGW_CRED_PATH or DCGW_ALLOW_LIST_PATH did not contain the appropriate file. |
Use the command readlink -f to verify the correct, complete path of credentials.json or destination_allow_list.yaml. |
When the installation has succeeded, either delete credentials.json and destination_allow_list.yaml or back them up to a secure location. The installer copies them to /var/opt/c1ws-dcgateway/conf/credentials.json and /var/opt/c1ws-dcgateway/conf/destiantion_allow_list.yaml with correct permissions. You do not need to keep the original files.
Once the data center gateway is successfully running, you can continue with Add a VMware vCenter to Workload Security or Add Active Directory computers.
Troubleshooting
Verify the status of the data center gateway
To determine if the data center gateway is active (its process is running), use SSH or Remote Desktop to connect to its server and then enter one of the following commands:
journalctl -u c1ws-dcgw.service -f
or:
systemctl status c1ws-dcgw
It should display the status, and which vCenter or Active Directory servers have been added:
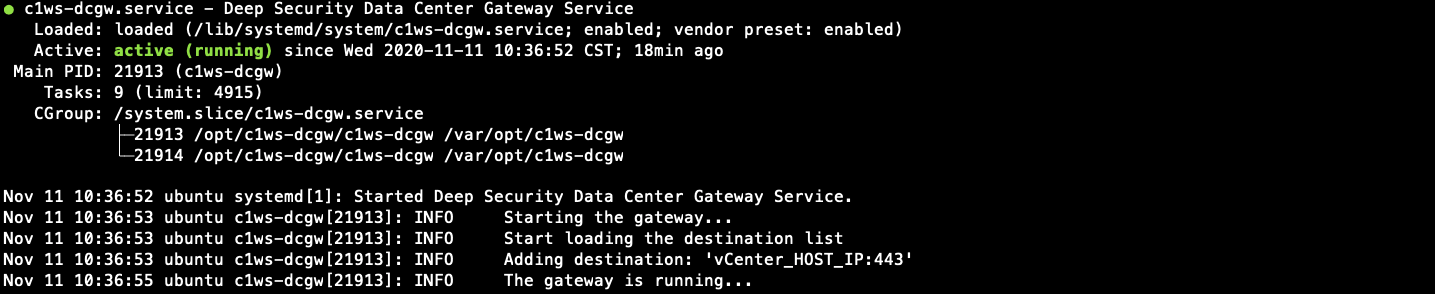
Status only shows which servers have been added to the list of destinations. It does not test the network connections with vCenter or Active Directory, which must be done separately.
Also enter the following command to verify that the error log is empty:
less +G c1ws-dcgw-error.log
Verify the network connections for a data center gateway
To verify that vCenter or Active Directory server's port is open and that it is reachable from the data center gateway, log into the data center gateway server and enter the following command:
nc -v SERVER_HOST_IP SERVER_HOST_PORT
Where:
SERVER_HOST_IPis the hostname or IP address of the vCenter or Active Directory server.SERVER_HOST_PORTis the listening port number. By default, it is 443 for vCenter, and 389(StarTLS)/636(LDAPS) for Active Directory.
The connection test should succeed.

If it does not succeed, verify that the port number is open. Also verify DNS settings and any routers, firewalls, and proxies between them. If there is a proxy, the connection must succeed to the proxy, not directly to the vCenter or Active Directory server.
If the connection test shows that the servers are reachable, but Workload Security is still not receiving data, then examine the data center gateway error log and logs that show connection attempts:
less +G c1ws-dcgw.log
It should show connection attempts to both vCenter or Active Directory servers (destination) and Workload Security FQDNs. Verify the configured host names and port numbers.

Upgrade the data center gateway
On the server where you want to upgrade the data center gateway, upload the RPM or DEB file, and then enter the upgrade command:
- On Red Hat Enterprise Linux:
sudo rpm -U <new data center gateway installer rpm> - On Ubuntu Linux:
sudo apt --only-upgrade install ./<new data center gateway installer deb>
To verify that the upgrade is complete:
- Check the data center gateway status and data center gateway network connections.
- Verify the version number of the installed software:
- On Red Hat Enterprise Linux:
rpm -q --info <data center gateway package name> - On Ubuntu Linux:
apt show <data center gateway package name>
