Topics on this page
What is File Storage Security?
Trend Micro Cloud One™ – File Storage Security provides anti-malware scanning on files in cloud storage services such as Amazon Web Services (AWS), Azure, and GCP.
Scan engine
The File Storage Security scan engine can scan of all sizes and types of files. File types include .BIN, .EXE, .MP4, .PDF, .TXT, .ZIP and more.
File Storage Security can detect all types of malware including viruses, trojans, spyware, and more. The engine is also able to search for obfuscated or polymorphic variants of malware, based on fragments of previously seen malware and detection algorithms.
How it works
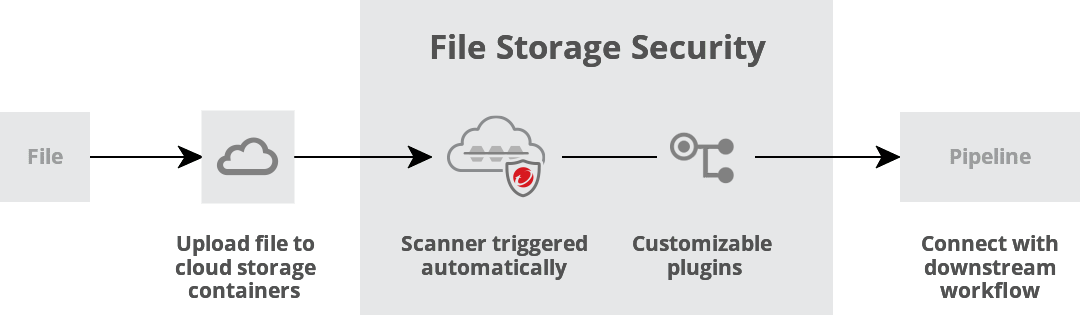
When a user or program uploads a file to a designated cloud storage container, File Storage Security performs a scan. The scan is performed only on the added file, not on existing resources in the storage container. When the scan is complete, your custom plugins or Lambdas take the scan results and connect with your downstream workflow for further processing. For details, see Architecture and flow
Files never leave your environment.
How long do scans take?
Scan time depends on the file size and type, and can range from around 3 to 25 seconds. For details, see Performance metrics (scan times).
How does the solution scale?
Because the File Storage Security scanner is a serverless function, it can handle multiple scans concurrently, and will scale up (or down) automatically in response to increases (or decreases) in load. For details, see Performance and scaling.
Stack contents
File Storage Security provides easy deployment using AWS CloudFormation, Microsoft Azure Resource Manager templates, or GCP Cloud Shell to integrate automated scans into your CI/CD pipeline. You can review these templates to see what resources make up each stack.
The template files are available for review on GitHub, here:
https://github.com/trendmicro/cloudone-filestorage-deployment-templates
Internet connections in a scan flow
When the scanner communicates, it involves three kinds of connections to the Internet via HTTPS port 443:
- Connection to Trend Micro Global Smart Protection Server (c1fss1.icrc.trendmicro.com)
- Connection to various cloud storage services, such as the AWS S3, SQS, and SNS services
-
Connection to File Storage Security telemetry service endpoint (filestorage.
CLOUD_ONE_REGION.cloudone.trendmicro.com/api/telemetry)The
CLOUD_ONE_REGIONin the endpoint is decided according to the Cloud One Region parameter of the deployment templates.