Topics on this page
AWS architecture and flow
This section illustrates the File Storage Security architecture, shows how information flows through the architecture during a scan operation, and describes each of the components in detail.
Topics:
Architecture
The following architecture diagram illustrates the main File Storage Security components and information flow.
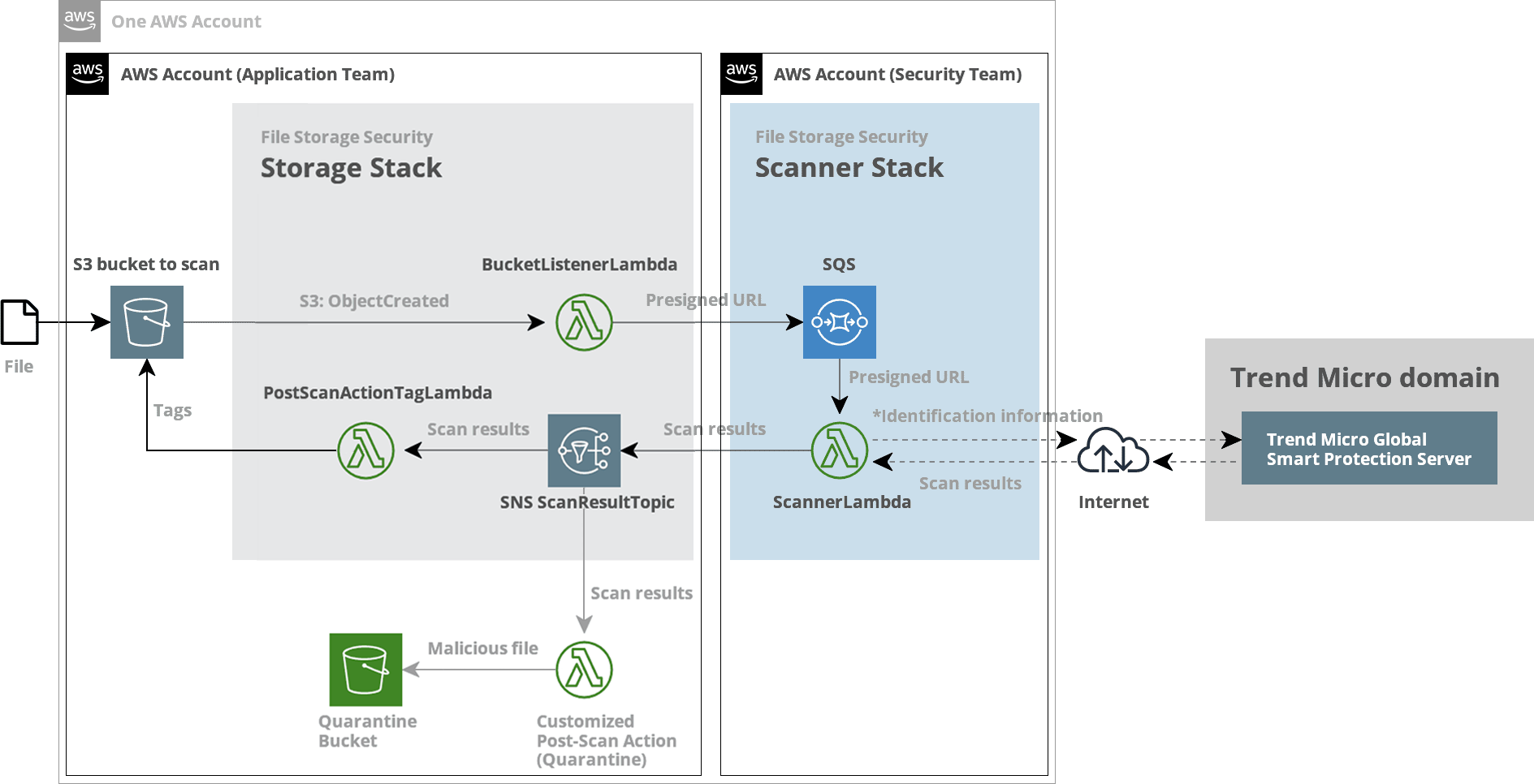
Information flows through this architecture as follows:
- A user or program uploads a file to the S3 bucket to scan. The upload generates an
s3:ObjectCreated:*event. - The BucketListenerLambda detects the
s3:ObjectCreated:*event, and sends a presigned URL to the SQS ScannerQueue in the scanner stack. The presigned URL links back to the file that needs to be scanned. - The ScannerLambda function, which is subscribed to the SQS ScannerQueue, does the following:
- Retrieves the presigned URL message from the SQS ScannerQueue.
- Checks the digital signature on the URL to make sure it's valid.
- Finds the file in S3 at the presigned URL location.
- Performs scanning on the file.
- Generates file identification information.
- Sends the file identification information to the Trend Micro Global Smart Protection Server in the cloud.
- The Trend Micro Global Smart Protection Server leverages the Trend Micro Smart Protection Network (not shown in diagram) to perform the remaining scanning on the file identification information (not the file). The scan results are returned to the ScannerLambda.
- The ScannerLambda does the following:
- Publishes the scan results to the SNS ScanResultTopic in the storage stack.
- Sends the scan results to the File Storage Security console. (The console is not shown in the diagram).
- The SNS ScanResultTopic notifies its subscribers that new scan results are available. Its subscribers are:
- the File Storage Security's PostScanActionTagLambda function
- your custom post-scan action Lambda function
- After receiving the SNS notification:
- The PostScanActionTagLambda function adds the scan results to the file using AWS tags and displays the results on the Scan Activity page. For details, see Understand tags and scan results.
- Your custom post-scan action Lambda function acts on the scan information provided in the SNS ScanResultTopic. For example, it might quarantine or delete the file if it is found to be malicious.
Components
S3 bucket to scan
The S3 bucket to scan is the bucket that is monitored for incoming (added) files. All files added to this bucket are scanned.
Presigned URLs
File Storage Security leverages the Amazon S3 presigned URLs to retrieve files from S3. Comparing with granting permissions with IAM, presigned URLs have the following advantages:
- The permissions are limited to the files that are uploaded and will expire after a set period of time.
- Enables the cross-account architectural option to deploy scanner and storage stacks in different AWS accounts.
Presigned URLs further limit the permissions to the least scope while allowing more deployment options. However users who have acquired the presigned URLs can access the file without being authenticated.
Therefore, File Storage Security treats and protects presigned URLs as secret throughout the scan process, including but not limited to encrypting the presigned URLs in transit or at rest.
For more information, see Using presigned URLs.
Storage stack
The storage stack monitors the S3 bucket to scan for incoming (added) files and sends them to the scanner stack for scanning. The storage stack can be deployed:
- as a standalone stack, using the storage stack CloudFormation template, or
- as a nested stack under the all-in-one stack.
For information on how many storage stacks you should use in your deployment, see How many stacks should I add?
Scanner stack
The scanner stack scans files and publishes the results to the SNS ScanResultTopic. The scanner stack can be deployed:
- as a standalone stack, using the scanner stack CloudFormation template, or
- as a nested stack under the all-in-one stack.
A typical File Storage Security deployment only needs one scanner stack, but if you think you might need more, see How many stacks should I add?
All-in-one stack
The all-in-one stack is deployed using the all-in-one CloudFormation template. The all-in-one stack includes:
- the scanner stack
- the storage stack
- supporting resources
BucketListenerLambda function
The BucketListenerLambda function is part of the storage stack, and is responsible for monitoring the S3 bucket to scan for added files and sending scanning requests to the scanner stack.
ScannerLambda function
The ScannerLambda function is part of the scanner stack and is responsible for scanning files and then sending file identification information to the Trend Micro Global Smart Protection Server for further scanning.
SQS ScannerQueue
The Amazon Simple Queue Service (SQS) ScannerQueue is part of the scanner stack, and is the queue to which the BucketListenerLambda sends its scanning request messages.
SNS ScanResultTopic
The Amazon Simple Notification Service (SNS) ScanResultTopic is part of the storage stack, and is the topic to which the scanner stack publishes its results. You can subscribe your custom post-scan action Lambda function to this topic to be notified of new scans.
PostScanActionTagLambda function
The PostScanActionTagLambda function is part of the storage stack, and is responsible for tagging the scanned file with its associated scan results.
Your AWS account
Your AWS account is where you'll be installing the File Storage Security stacks. You can install the stacks into multiple accounts if you want. For details, see the multi-stack architecture.
Custom post-scan action Lambda function
The custom post-scan action Lambda function is a function that you write. It is responsible for processing scan results that it obtains from the SNS ScanResultTopic. For details, see Create post-scan actions.
API and code samples
We provide APIs and code samples that you can use to create your Lambda functions. See Create post-scan actions for details.
Console
The console is a web interface where you can view scan results and deploy stacks. The console is hosted by Trend Micro and exists outside your AWS account.
Additional Lambda functions
File Storage Security uses several other Lambda functions in its operation. These include:
-
SetupBucketNotificationLambda sets up the bucket notification of an ObjectCreated event. This allows File Storage Security to monitor file uploads.
-
CreateLambdaAliasLambda creates a File Storage Security managed Lambda function alias. This allows you to adjust concurrency on it.
-
ScannerDeadLetterLambda handles the dead letter message that the ScannerLambda fails to handle. This function sends the telemetry to File Storage Security.
-
GetLambdaLastConfig preserves the configurations of the Lambda functions from being overwritten during a stack update.