Topics on this page
Malicious payload
The Malicious Payload policy protects your computers from known and zero-day vulnerability attacks as well as against SQL injections attacks, cross-site scripting attacks, and other web application vulnerabilities. The Malicious Payload policy rules define a set of conditions that are compared to the payload session and application layers of network packets (such as HTTP/HTTPS), as well as the sequence of those packets according to those higher-layer protocols.
Configure the malicious payload policy
- Select the group.
2.In the left pane menu, click ![]() .
.
-
Ensure that Malicious Payload is enabled.
-
Set the state to Report. This will trigger events without blocking the request, which allows you to run your application and see which expected behaviors trigger malicious payload events.
-
In the right pane, click
 .
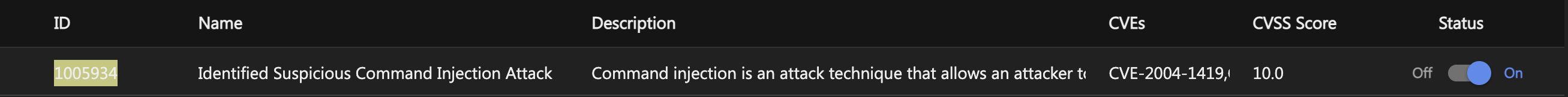
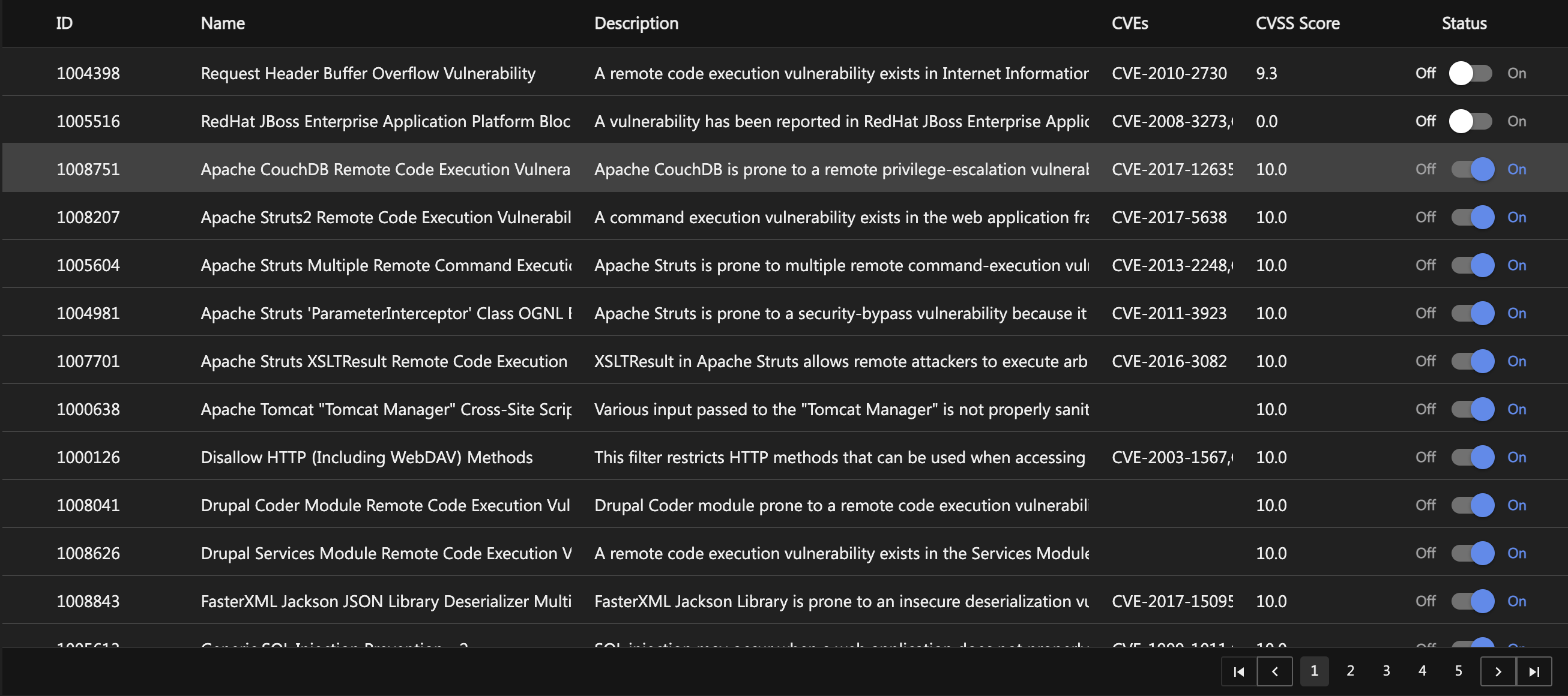
.The list of malicious payload rules are displayed with the rule's ID, name, description, and Common Vulnerability Scoring System (CVSS) score, if applicable. If you'd like to read the full description of the rule or see the rule's CVSS score, select the desired rule. Use the search bar in the top-right corner to search for specific malicious payload rules.
-
In the Malicious Payload Policy Configuration window, select the Include Malicious Payload data in report option to send the HTTP/HTTPS message payload to the server when alerts are raised.
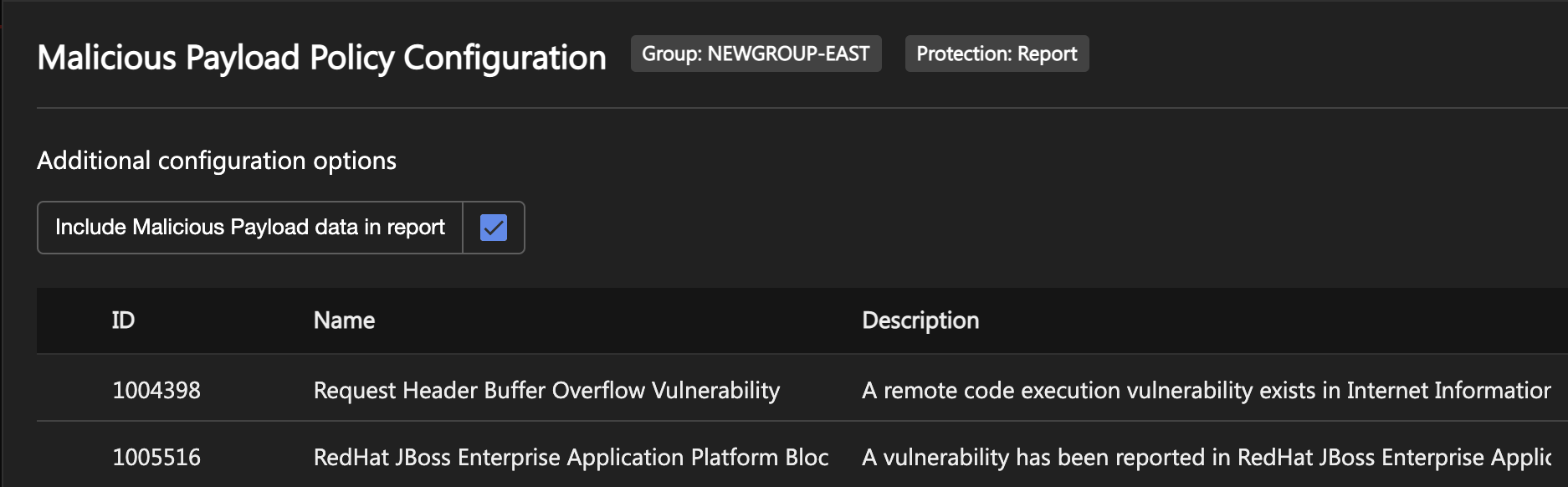
When the option is selected, the agent includes the HTTP/HTTPS message payload in the alert details. In the case where there are concerns of sensitive information in the HTTP/HTTPS payload being persisted, such as Personally Identifiable Information (PII), the option can be deselected and the HTTP/HTTPS message payload won't be included in the alert details. By default, the payload is included.
-
Turn the individual rules off or on by setting the toggle.
-
Click Save Changes.
-
Close the window.
By default, all of the malicious payload rules are turned on to best protect your application.
-
Navigate to your application and use it in the various scenarios that it was designed to handle.
-
On the Application Security dashboard, check the Events page for malicious ayload events. If one has been triggered, follow the steps in Manage malicious payload events.
-
Once you're happy with your policy configuration and events are no longer being triggered by expected behavior, go to Your Group > Policies > Malicious Payload.
-
On the right of Malicious Payload, set the state to Mitigate. When a rule is triggered, the attempt will be blocked and a malicious payload event will appear on the Dashboard.
Malicious payload events
Malicious payload events are displayed on the Dashboard in Events or Filter by Group > Your Group.
Every event includes the Request Details panel for general information about the event. For more information, see Manage events.
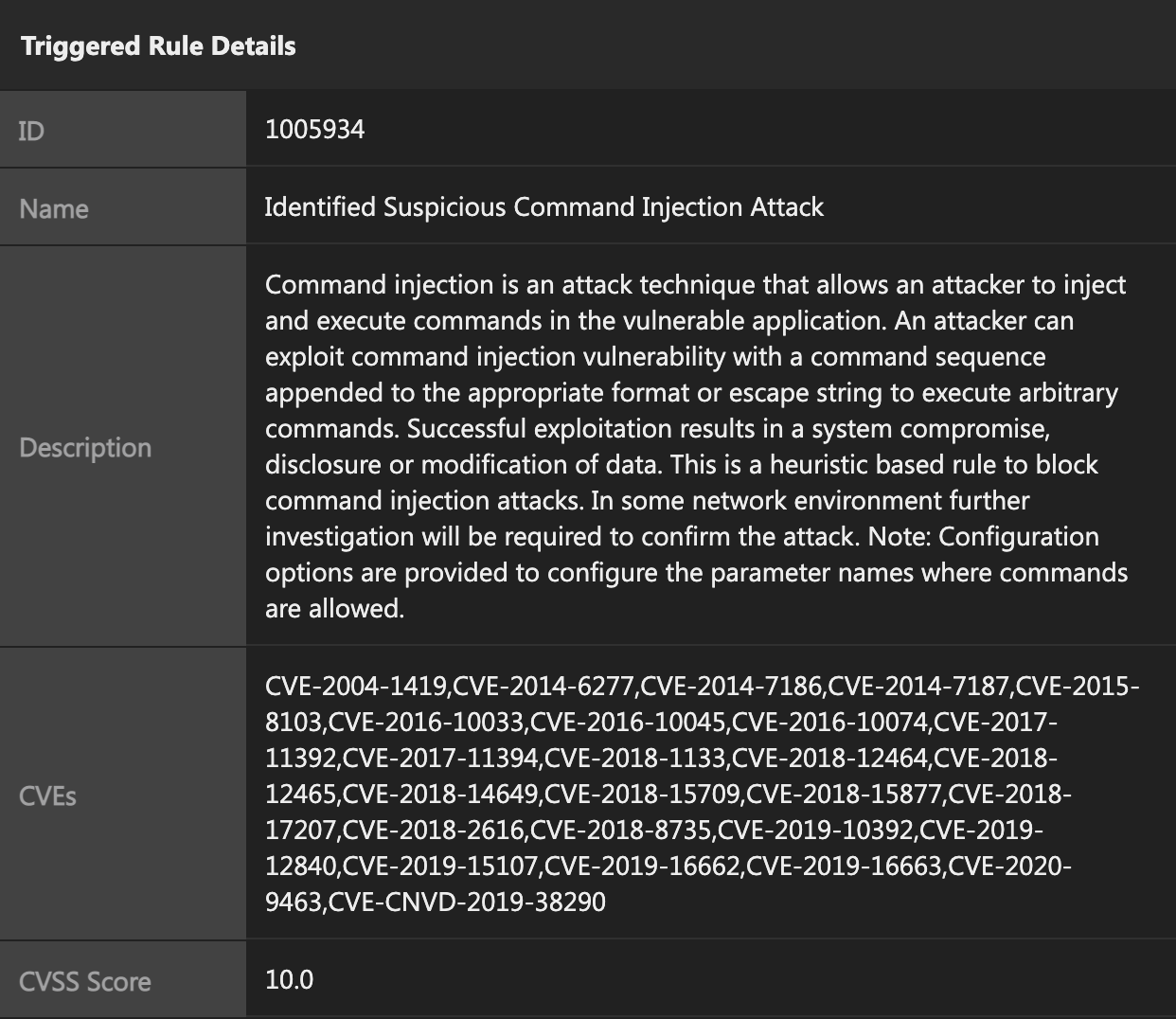
Under Triggered Rule Details, the following information is displayed:
- ID: The ID number of the rule that was triggered.
- Name: The name of the rule that was triggered.
- Description: The description of the rule that was triggered.
- CVEs: The CVEs (Common Vulnerabilities & Exposures) entry.
-
CVSS Score: The CVSS (Common Vulnerabilities Scoring System) score.
Under Payload Details, the following information is displayed:
- Position: The position in the HTTP/HTTPS stream where the attack payload was detected.
- Stream Position: The offset in the displayed bytes where the attack payload was detected.
- Payload: The payload where the vulnerability exists.
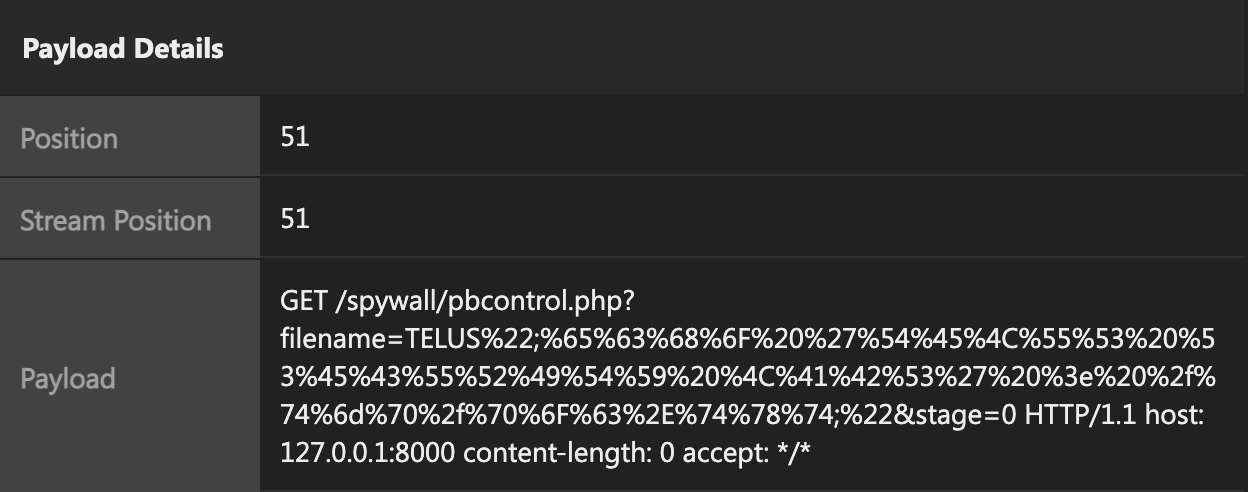
Payload details are available only if the Include Malicious Payload data in report option in the Malicious Payload Policy Configuration window was selected at the time that the alert was raised.
Manage malicious payload events
If Application Security is reporting malicious payload events:
- Modify your code so a malicious payload attack can not be leveraged in the future.
-
If the event was triggered by an expected behavior of your application and you'd prefer not to modify your code and allow the behavior, select Click to Manage Policy. In the Alert section, you can see what policy rule was triggered. If you'd like to allow this behavior on your application, toggle the rule OFF.