Topics on this page
Illegal file access
Application Security protects your application against illegal file access by blocking attackers from reading or writing to your private files.
Configure the illegal file access policy
- Select the group.
- In the left pane menu, click
 .
. - Ensure that Illegal FIle Access is enabled.
- Set the state to Report. This will trigger events without blocking the request, which allows you to run your application and see which expected behaviors trigger Illegal File access events.
- On the right of the page,click
 .
. - To allow write or read access to your application, select the respective blue button.
The button will turn grey to indicate it has been turned off.
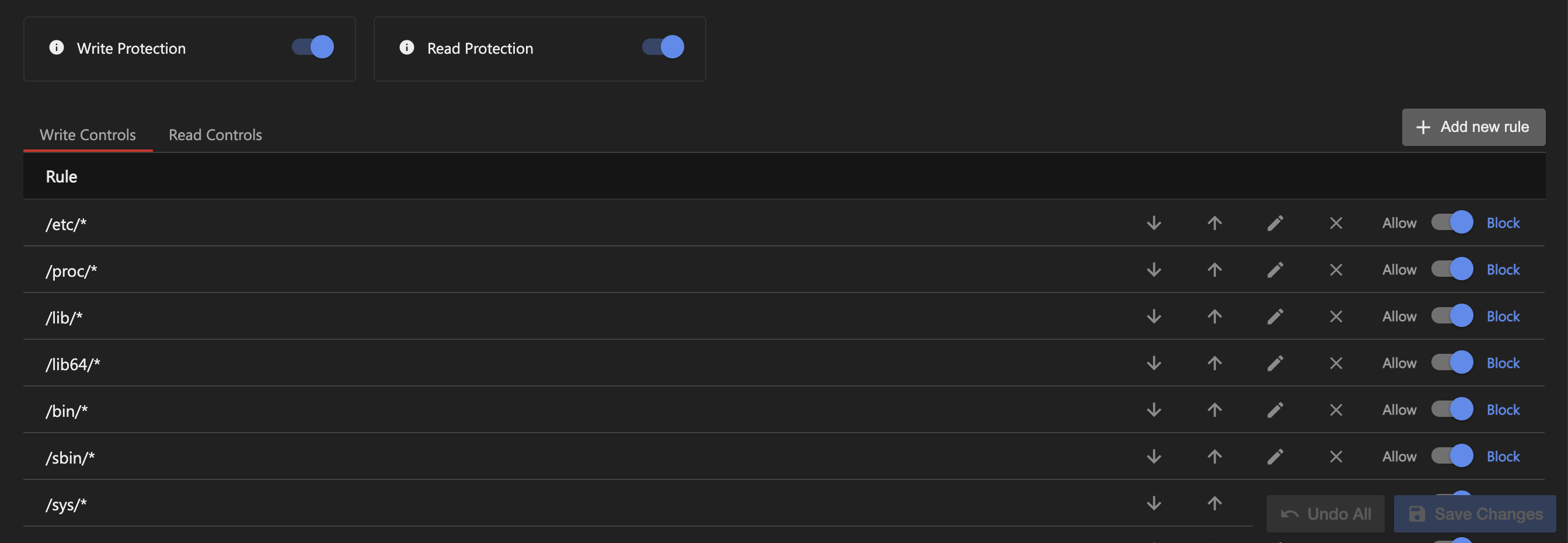
In the Illegal File Access Policy Configuration window are the Write Protection and Read Protection toggles. -
To allow access to each file or folder, select either Allow or Block.
You can also edit, delete, or reorganize the rules by selecting the grey arrow buttons on the left of the window.
Under Write Controls and Read Controls are a list of rules that consist of glob patterns for common file names.When creating a new group, the Illegal File Access policy includes a set of predefined defaults. For the Write Control algorithm, the default policy prevents writing files to critical system folders as well as files that could impact the web application integrity. Other files are allowed to be written. For the Read Control algorithm, the defaults allow all web application resource files, such as images, JSP files, etc., to be read. Review the default rules to ensure they are relevant for the application to protect.
-
Select Save Changes and close the window.
- Navigate to your application and use it in the various scenarios that it was designed to handle.
- On the Application Security dashboard, check the Events page for Illegal File Access events. If one has been triggered, follow the steps in Manage Illegal File Access events.
- Once you're happy with your policy configuration and events are no longer being triggered by expected behavior, go to Your Group > Policies > Illegal File Access.
- On the right of Illegal File Access, set the state to Mitigate. When a rule is triggered, the attempt will be blocked and an Illegal File Access event will appear on the Dashboard.
Add a new illegal file access rule
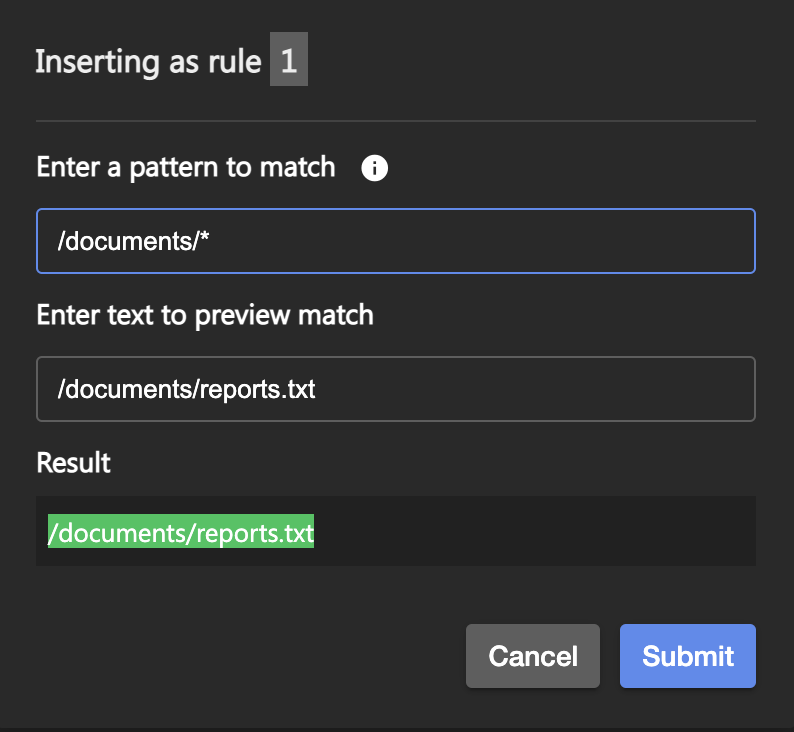
- Select Add new rule button on the right of the Illegal File Access Policy Configuration window.
- Under Enter a pattern to match, enter the glob pattern that matches your file path.
- Under Enter text to preview match, enter the actual file path and name of the file you want protected. If the glob pattern you entered above is the correct pattern and encompasses the file, the file name will be highlighted in green under Results. If the file name is grey, correct your glob pattern.
-
Select Submit to save the rule.
Delete an illegal file access rule
- In the row containing the rule to delete, select the X icon.

- Select Save Changes and close the window.
Illegal file access events
Illegal File Access events are displayed on the Dashboard on the Events page or in your respective Groups's dashboard.
Every event includes the Request Details panel for general information about the event. For more information, see Manage Events.
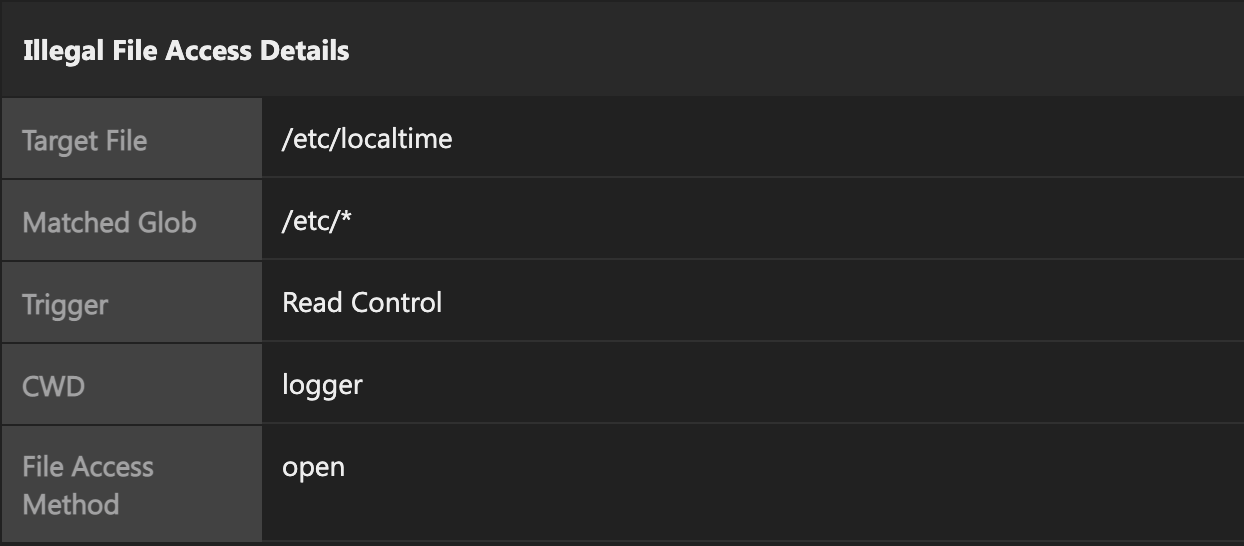
Under Illegal File Access Details, the following information is displayed:
- Target File: The file that was targeted
- Matched Glob: The glob pattern that was matched and triggered the event
- Trigger: Whether read or write access was attempted
- CWD: The current working directory.
- File Access Method: The file access method that was attempted
Manage illegal file access events
If Application Security is reporting illegal file access events:
-
In the top right corner, select View Stack to see where in your code the attack was leveraged.
-
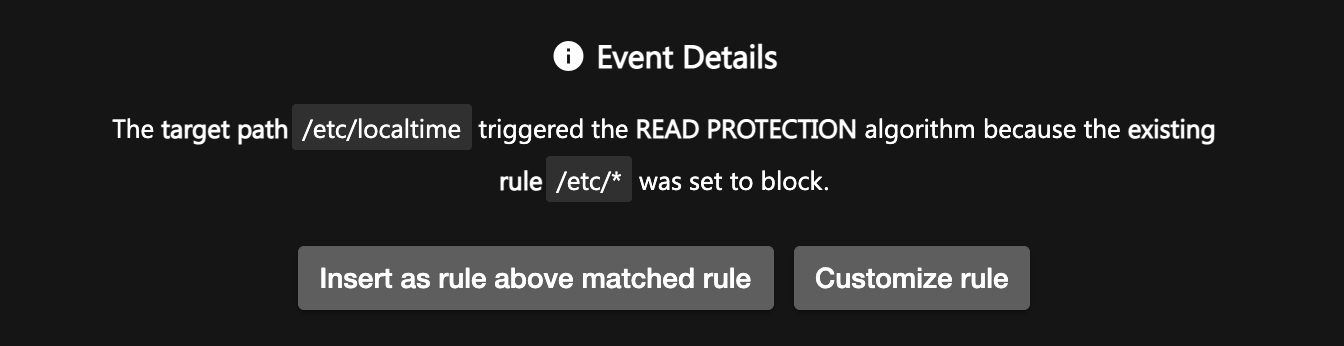
If you would like to allow write or read access to the file that triggered the event, select Click to Manage Policy.
-
In the Alert section, you can see the path of the targeted file, the protection that was triggered, and the existing rule that blocked access to the file. Select Insert as rule above matched rule to automatically add the glob pattern for the file. This will create an allow rule for that file, so you have read or write access to it in the future. If you'd like to edit the glob pattern, select Customize rule and Submit when you're finished.